What is Token-Based Authentication?

- Share:





2938 Members
Token-based authentication is a crucial aspect of software development every developer should be familiar with. This article takes a deep dive into the world of token-based authentication, looking at why it's so important and how it's become a must-have for modern app development.
Token-based authentication systems are changing the way we think about security, taking a step up from session-based methods, offering a more flexible, secure, and scalable solution. This concept is especially crucial in today's reality of distributed apps and cloud computing. The fact that token-based authentication is so popular just goes to show how effective it is and how much digital security needs have evolved in app development.

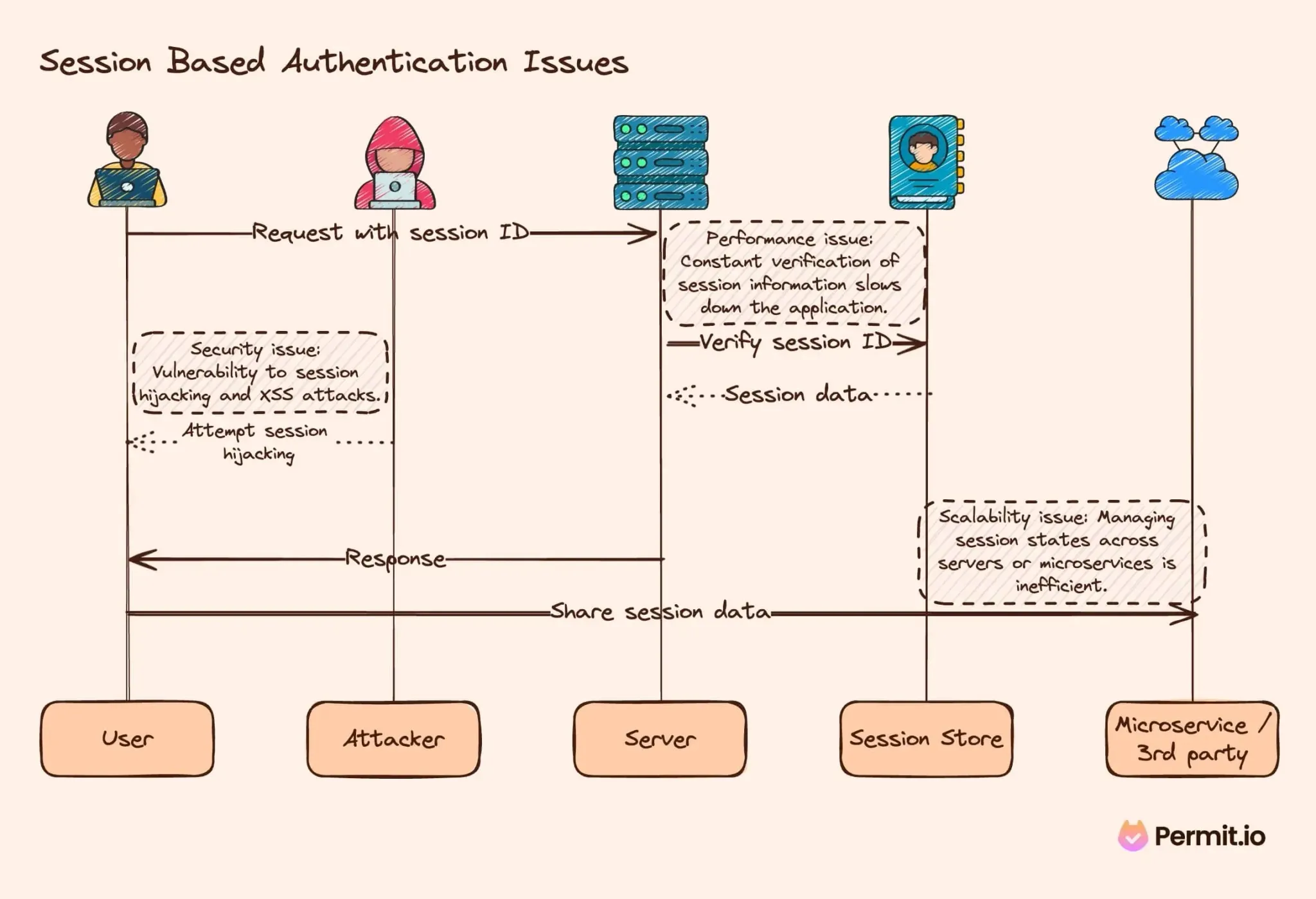
In the traditional session-based authentication mindset, the server maintains the state of the user's session, typically using a session ID stored in a cookie. While functional for simpler, monolithic applications, this model shows its limitations in the face of modern, distributed applications. These limitations manifest in several ways:
Token-based authentication addresses these issues by offering a stateless approach. Each token encapsulates the user's identity and permissions, eliminating the need for the server to maintain the session state. This approach doesn’t just simplify the architecture but also enhances security. Tokens, especially when implemented using standards like JWT (JSON Web Tokens), provide strong security features like signing and optional encryption, improving their security against various exploits.
Token-based authentication is not just a technical concept; it's really a fundamental shift in how users and sessions are managed. Simply put, it's like a 'digital pass' that confirms your identity and permissions in a system without the constant need for username and password verification. This pass, or token, can be presented each time a user makes a request, ensuring security without the overhead of traditional methods.
The rise of standards such as OAuth and JWT (JSON Web Tokens) has been instrumental in shaping the landscape of token-based authentication. OAuth provides a framework for authorization, allowing services to verify identities without directly handling user credentials. Meanwhile, JWT has become the de facto standard for tokens, thanks to its compact, URL-safe format and ability to carry a payload of claims. These claims can include user identity, roles, and any other pertinent information, all in an easily verifiable and secure format. These standards have streamlined the implementation of token-based authentication and enhanced compatibility across different systems and services.
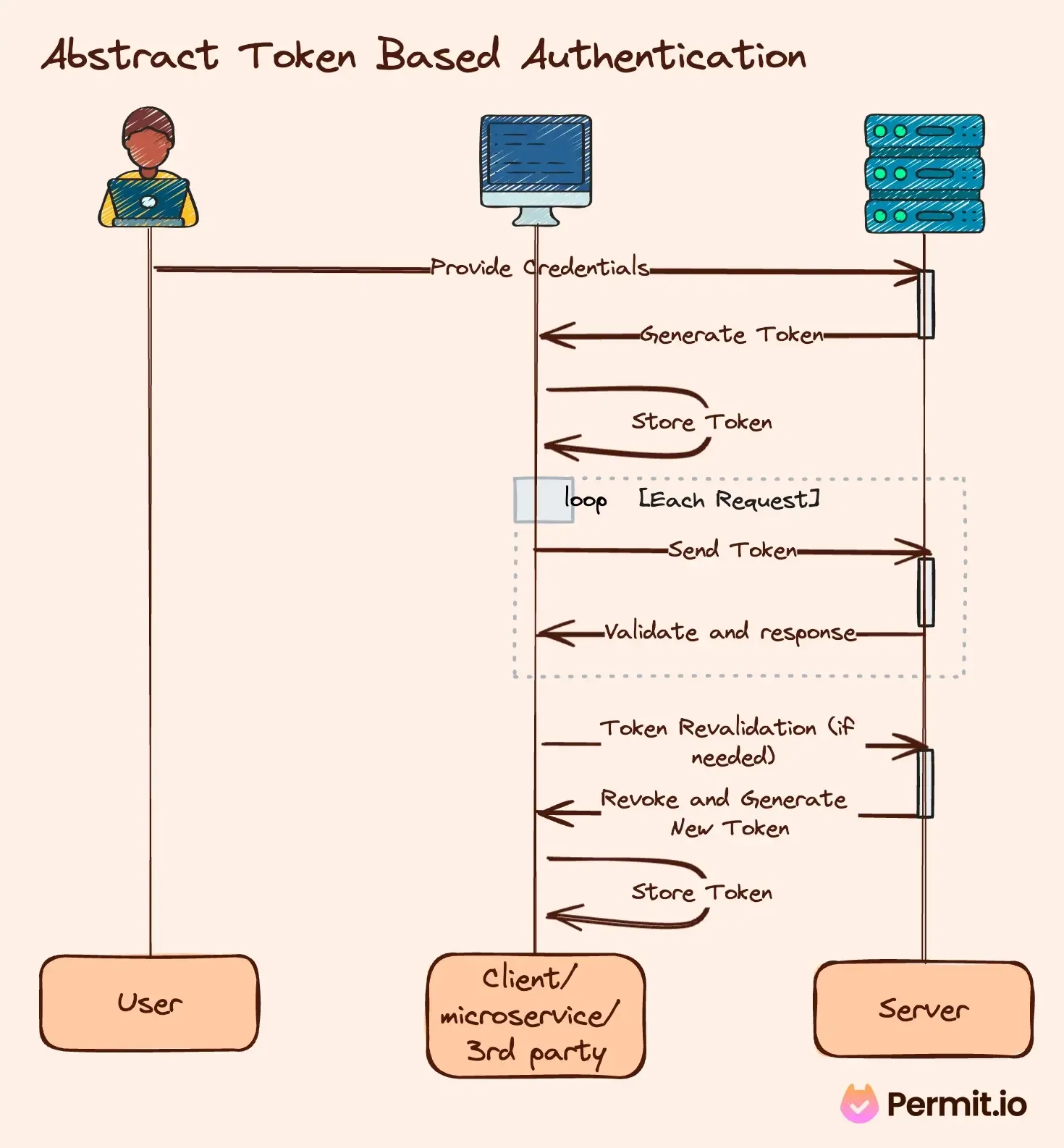
The mechanics of token-based authentication revolve around token creation, distribution, and validation. Here's an overview of the process:
An example in pseudo-code might look like this:
// User login
const userToken = authenticateUser('username', 'password');
storeTokenLocally(userToken);
// Making an authenticated request
const storedToken = retrieveToken();
makeRequestWithToken('/api/data', storedToken);
// Server-side token validation
function validateRequest(request) {
const token = extractToken(request);
if (verifyToken(token)) {
return processRequest(token);
} else {
return 'Invalid token';
}
}
In this example, authenticateUser generates a token upon successful login, storeTokenLocally stores the token, retrieveToken and makeRequestWithToken manages the sending of the token with requests and validateRequest handles token verification server-side.
Diving deeper into token-based authentication, we encounter various types of tokens, each serving specific roles in the authentication and authorization process.
Let's consider an example where a user is authenticated via OAuth 2.0:
// After successful authentication
const accessToken = getAccessToken();
const refreshToken = getRefreshToken();
// Accessing a protected resource
makeApiCall('/api/userdata', accessToken);
// Refreshing an expired access token
if (isTokenExpired(accessToken)) {
accessToken = refreshAccessToken(refreshToken);
}
In this snippet, getAccessToken and getRefreshToken obtain the respective tokens, makeApiCall uses the access token to request data, and refreshAccessToken is used to obtain a new access token using the refresh token.
While token-based authentication offers numerous advantages, it also comes with its own challenges that developers must navigate.
Addressing these challenges often requires a combination of coding best-practices, employing token rotation and revocation strategies, and implementing efficient token validation mechanisms.
In authorization (the process of deciding if a user is allowed or denied to perform an operation after logging in), tokens can be used as a source of more information about the user. There are two common standards to store data for authorization in tokens.
Using scopes and claims only to authorize requests can end up with a mess of code that couples application policy with business logic code, making it hard to maintain and audit. The pattern of using imperative if statement and condition functions in the code instead of using them in the right scopes can end up with endless pull requests for simple authorization changes.
This anti-pattern can be illustrated with an example:
// A classic middleware authorizer function
function authorizeUser(token) {
const userClaims = decodeToken(token).claims;
if (userClaims.role === 'admin') {
return 'Full access granted';
} else if (userClaims.access_level === 'premium') {
return 'Premium features accessible';
} else {
return 'Basic access';
}
}
In this pseudo-code, decodeToken extracts claims from the token, and authorizeUser uses these claims to determine the level of access the user should have. When the product requirements change, we need to change the application code just for this simple policy decision.
The proper way to use scopes and claims is to combine them with a Policy-as-Code based authorization system.
Token-based authentication synergizes remarkably with the concept of 'Policy as Code'.
Policy languages and engines, such as Open Policy Agent (OPA) or AWS’ Cedar, empower developers to define security and operational policies in code. When coupled with token-based authentication, these policies result in a powerful, flexible system for controlling access to resources.
Here’s an example of how policy as code might work with token-based authentication:
const userToken = getUserToken();
const policyDecision = policyEngine.evaluate(userToken, 'accessResource');
if (policyDecision.allowed) {
grantAccessToResource();
} else {
denyAccess();
}
In this scenario, getUserToken retrieves the user’s token, and policyEngine.evaluate assesses this token against predefined policies to decide on resource access. When product requirements change, the only need is to change the policy itself, while application code and logic stay the same.
Authorization-as-a-service solutions like Permit.io allow you to take this integration of policy engines another step forward. Permit allows you to create intricate authorization policies with a no-code UI (Or API), which generates code for you and pushes any updates or changes to your application in real-time.
Embracing token-based authentication in your applications is more than just a security measure; it's a step towards more scalable, flexible, and secure systems. Services like Permit.io can significantly streamline the implementation of sophisticated authentication and authorization mechanisms in your applications.
Want to learn more about the world of IAM? Join our Slack community, where hundreds of devs are building and implementing authentication and authorization.

Application authorization enthusiast with years of experience as a customer engineer, technical writing, and open-source community advocacy. Comunity Manager, Dev. Convention Extrovert and Meme Enthusiast.