Cookies vs. Local Storage: What’s the Difference? When and Where to Use Each?
- Share:




2938 Members
Managing and storing data in the browser efficiently is a crucial aspect of building web applications in terms of performance, user experience, and security. Web developers often rely on client-side storage solutions like cookies and local storage to save user preferences, authentication tokens, and other essential data.
But what exactly is the difference between cookies and local storage? When should you use one over the other? And how do security concerns impact your choice?
Both cookies and local storage allow websites to store information on a user’s browser, but they serve different purposes and come with unique benefits and drawbacks. Understanding these differences can help you make informed decisions about which storage mechanism to use in various scenarios.
In this article, we’ll break down:
By the end, you’ll hopefully know exactly when to use cookies vs. local storage and how to make the right choice for your web applications.
You can watch our video version of this article here:
Without further adieu, let's get into it -
Web applications often need to store data in the browser to improve performance, maintain user preferences, and support authentication. Since HTTP is a stateless protocol, it does not track previous requests or responses. This means it requires storage solutions that allow websites to retain information across visits/interactions.
Client-side storage refers to methods that store data directly in a user’s browser rather than on a remote server. This reduces server load, speeds up access to frequently used data, and improves overall user experience. The two primary types of client-side storage are:
While cookies and local storage allow websites to store data, they serve different purposes. The next sections will explore these storage methods in detail, starting with local storage.
Local storage is a browser-based storage mechanism that allows web applications to store data in key-value pairs. Local storage data is not sent with every HTTP request (unlike cookies), making it more efficient for storing non-sensitive data on the client side.
Local storage is part of the Web Storage API and is accessible through JavaScript using the localStorage object. Data stored in local storage persists indefinitely unless manually removed by the user (or through JavaScript). This makes it useful for storing information that should persist across sessions, like user preferences, theme settings, or cached data.
JSON.stringify() and retrieved using JSON.parse().setItem() and getItem().Local storage is best suited for storing non-sensitive, client-side data that needs to persist across browser sessions. This means it isn’t suited for authentication or security-critical information.
Next, we’ll look at what cookies are.
Cookies are small text files that websites store in a user's browser to retain information across visits. Unlike local storage, cookies are designed to be accessible by both the client and the server, making them essential for authentication, session management, and tracking user behavior.
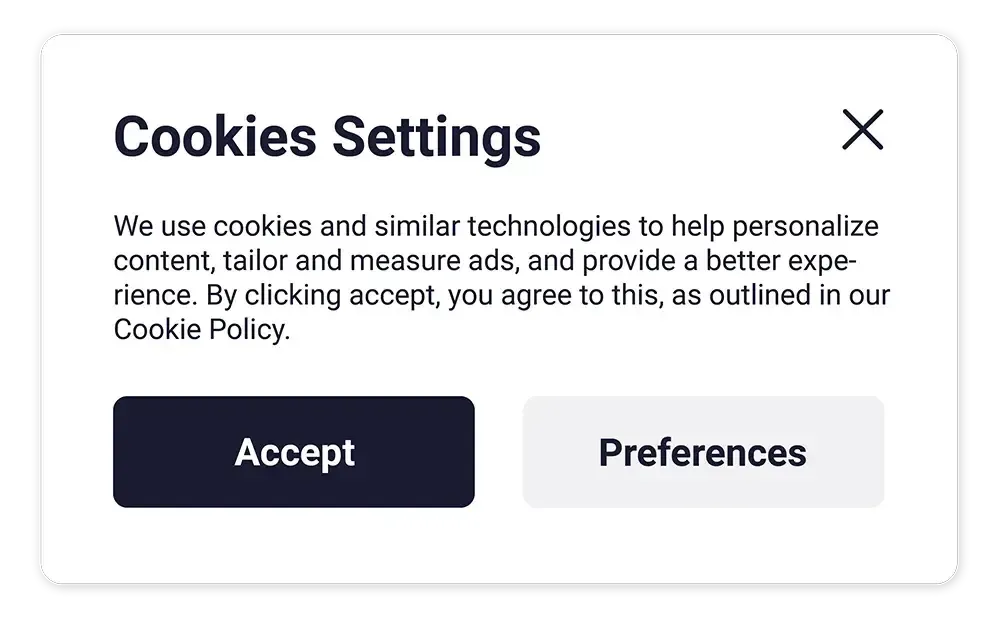
When a user visits a website, the server can send a cookie along with the HTTP response. The browser then stores this cookie and includes it in subsequent requests to the same domain. This allows the server to recognize returning users and maintain session data.
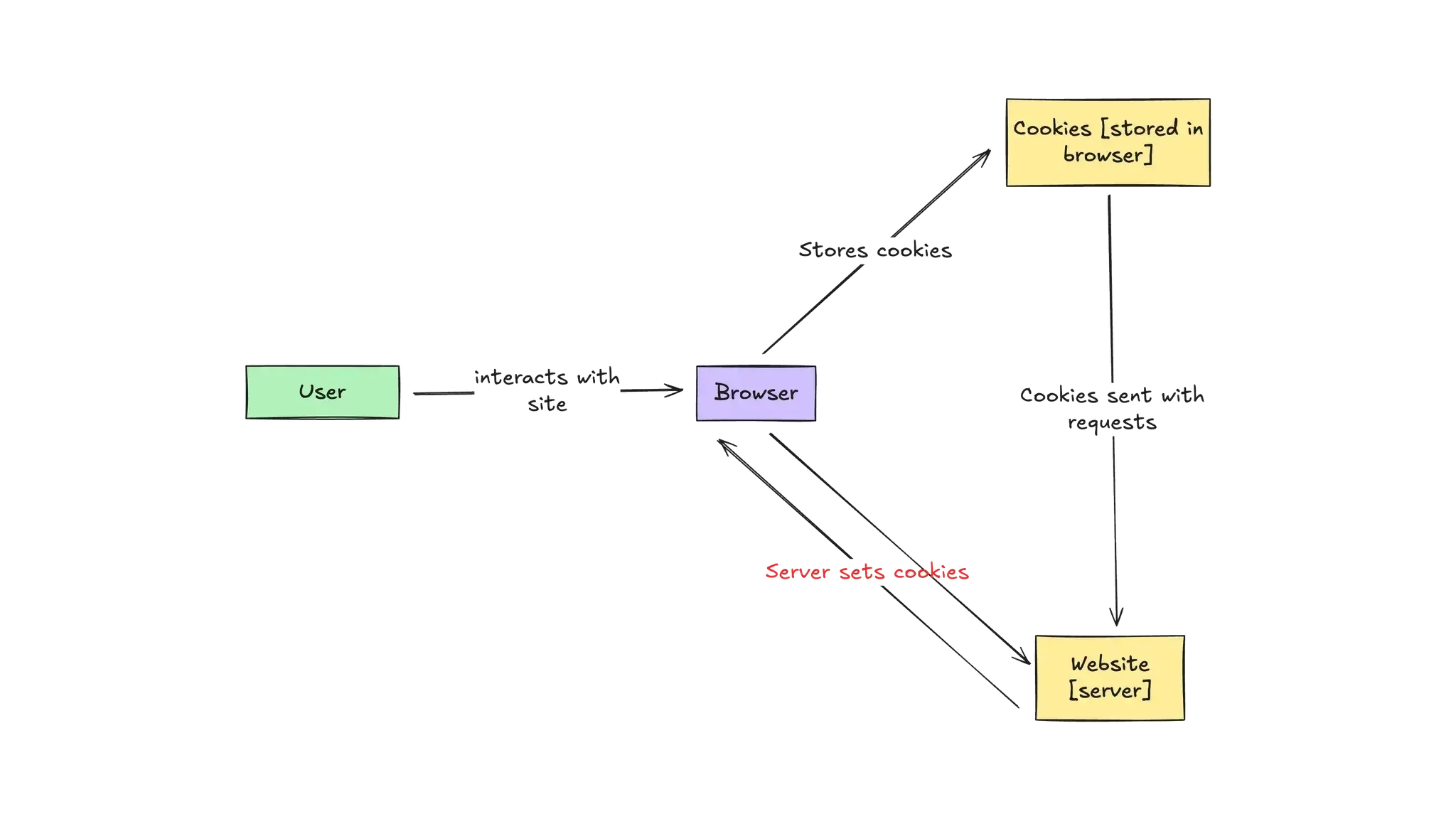
Cookies can be configured with different attributes, such as:
HttpOnly, Secure, SameSite) to enhance protection.Cookies are most effective for managing authentication, maintaining user sessions, and tracking user behavior. They should not be used for storing large or non-essential data due to their storage limitations and impact on performance.
Next, we’ll compare cookies and local storage side by side.
As covered in previous sections, both cookies and local storage allow websites to store data in a user's browser, but they differ in their use cases, performance, and security implications. Below is a direct comparison of the two:
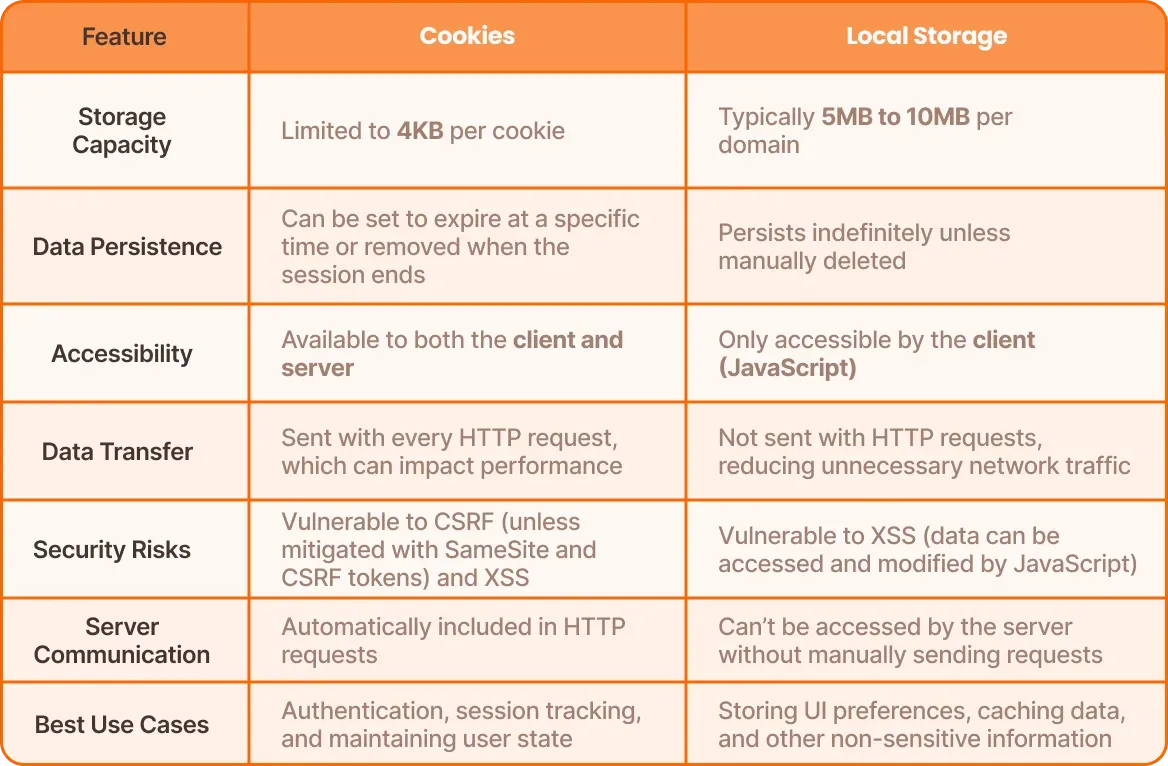
As we can see from the table above:
Considering this, let’s look at when to use cookies vs. local storage based on different scenarios.
Choosing between cookies and local storage depends on your application's needs. Here are some key scenarios that can help you determine when each storage method fits best:
HttpOnly, preventing JavaScript from accessing them and reducing exposure to XSS attacks.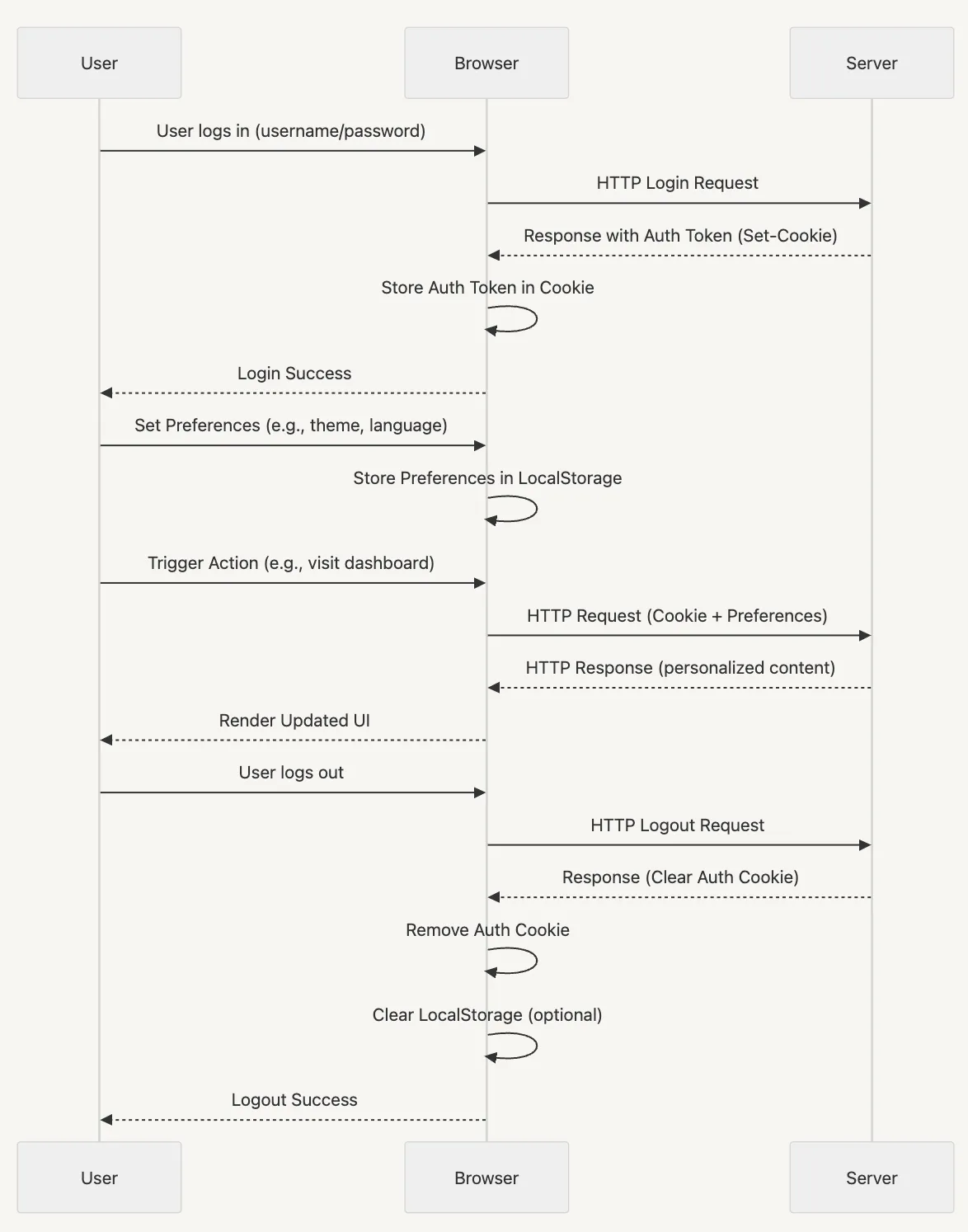
Security is a critical factor when deciding between cookies and local storage, especially when dealing with authentication, user sessions, or sensitive information. Both storage methods come with risks that must be properly managed.
One of the biggest challenges developers face is deciding where to store authentication and authorization data. Applications store authentication tokens in local storage or cookies, but this must be done carefully and securely.
Handling authorization data requires that applications have a way to manage user roles, permissions, and access control centrally rather than relying on client-side storage methods that can be manipulated or exploited.
Here are some security considerations to keep in mind in this context:
First of all - neither cookies nor local storage should be used to store sensitive information like passwords or authentication tokens without additional security measures. If local storage is used to store authentication tokens, it is vulnerable to XSS attacks. If cookies are not configured properly (HttpOnly, Secure, SameSite), they can be exploited through CSRF attacks.
For the safest authentication strategy, server-managed session tokens or secure HttpOnly cookies are preferred.
Beyond authentication, another major security challenge is how applications store and enforce user permissions and access control. Relying on local storage or cookies to keep track of user roles, permissions, or access levels comes with significant risks:
Applications need a centralized, server-side approach to managing user roles and permissions. This ensures that access control remains dynamic, secure, and manipulation-resistant.
Permit.io addresses these challenges by providing a structured way to handle authorization externally without exposing critical data in the browser. By moving access control logic to the backend, applications can:
Prevent unauthorized role modifications by ensuring that permissions are enforced by the server.
Dynamically update user access without requiring manual intervention or browser storage synchronization.
Eliminate security risks associated with storing authorization data in local storage or cookies.
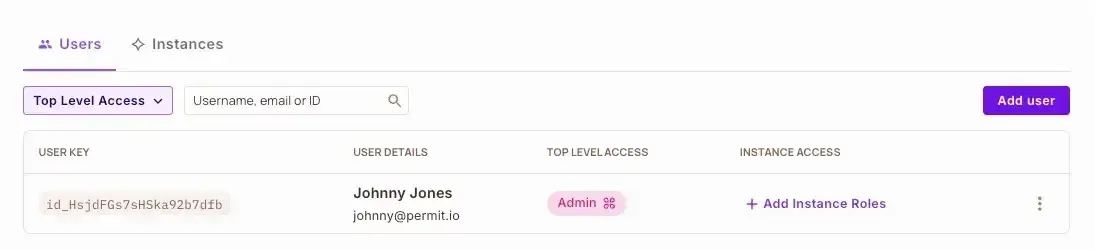
By handling authorization separately from authentication, applications gain a more secure, scalable, and flexible access control system that does not rely on insecure client-side storage.
Understanding the difference between cookies and local storage is a must for making informed decisions about data storage, authentication, and performance in web applications.
While cookies are best suited for authentication and session management, local storage provides a more efficient way to store non-sensitive client-side data without increasing network traffic.
When it comes to authorization data and access control, neither storage method is truly secure. Storing user roles, permissions, or access tokens in the browser can lead to security risks, privilege escalation, and data breaches.
A server-side authorization approach can ensure dynamic, centralized, and secure access control without exposing sensitive data to the client.
Got authentication or authorization questions? Join our Slack community

Application authorization enthusiast with years of experience as a customer engineer, technical writing, and open-source community advocacy. Comunity Manager, Dev. Convention Extrovert and Meme Enthusiast.
Developer Advocate at Permit.io, Software Engineer, and YouTube Creator