Best Practices for API Authorization

- Share:





2938 Members
APIs are crucial gateways to the information exchange process in the development world.
In this context, authorization plays an enormous role in ensuring these interactions are secure, reliable, and compliant with various privacy and data protection norms. It's not just about who can access your APIs but what they can do with them. Understanding and implementing solid authorization practices is essential for safeguarding sensitive data and maintaining the integrity of API interactions.
Effective API authorization relies on accurately identifying and catering to the diverse "actors" that interact with your APIs. Each type of actor requires specific authorization considerations to balance security and functionality. Let’s explore some of the key actors and their unique authorization needs:
Each of these actors plays a distinct role in the ecosystem of API interactions, necessitating tailored authorization strategies. By understanding and addressing the specific needs of these key actors, you can create a more secure, efficient, and user-friendly API environment.
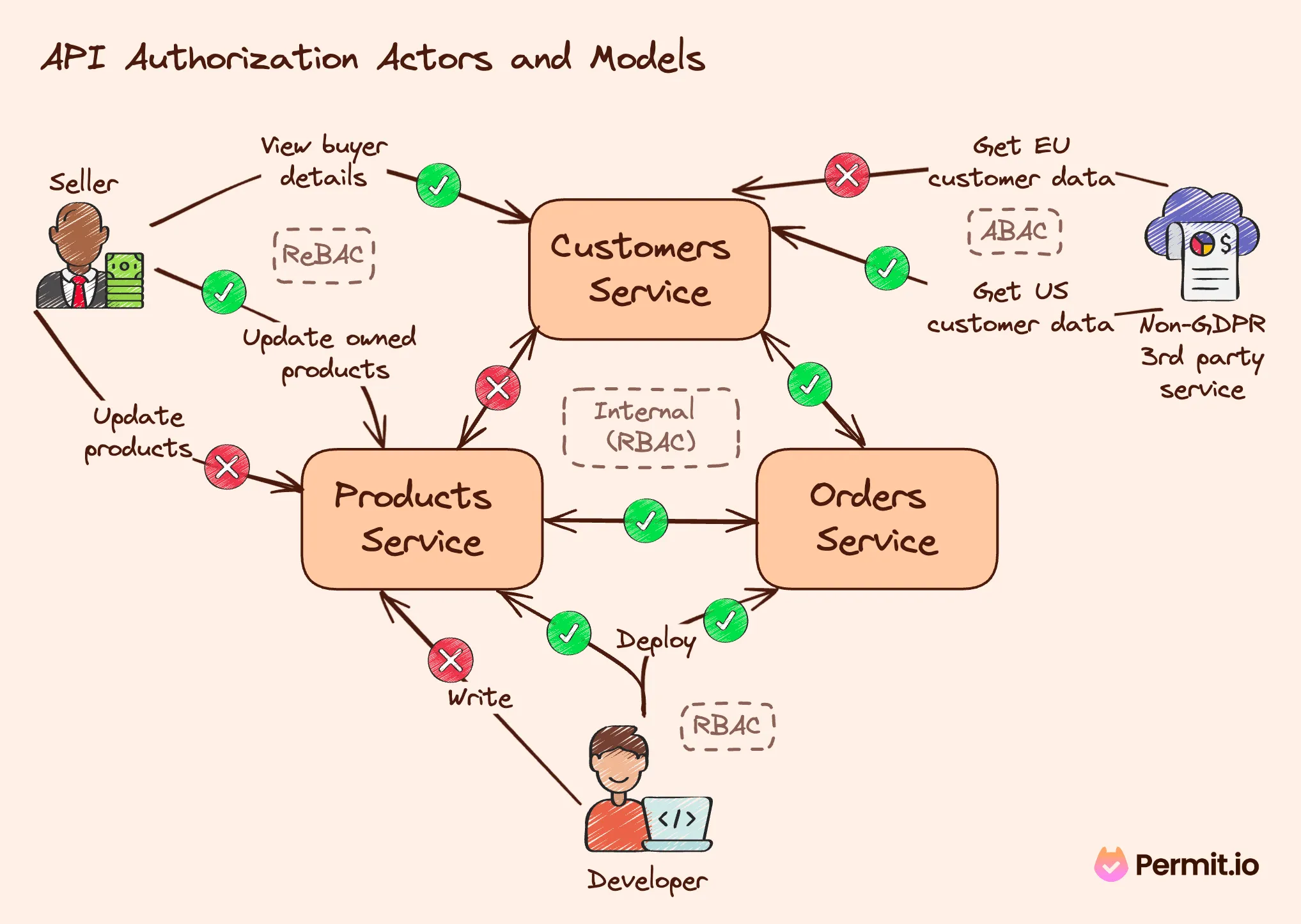
Authorization models provide the structure for managing and granting access permissions. Here are the three prominent models with their explanations and examples:
Choosing the right model or combination of models is crucial for establishing a flexible and secure API authorization strategy.
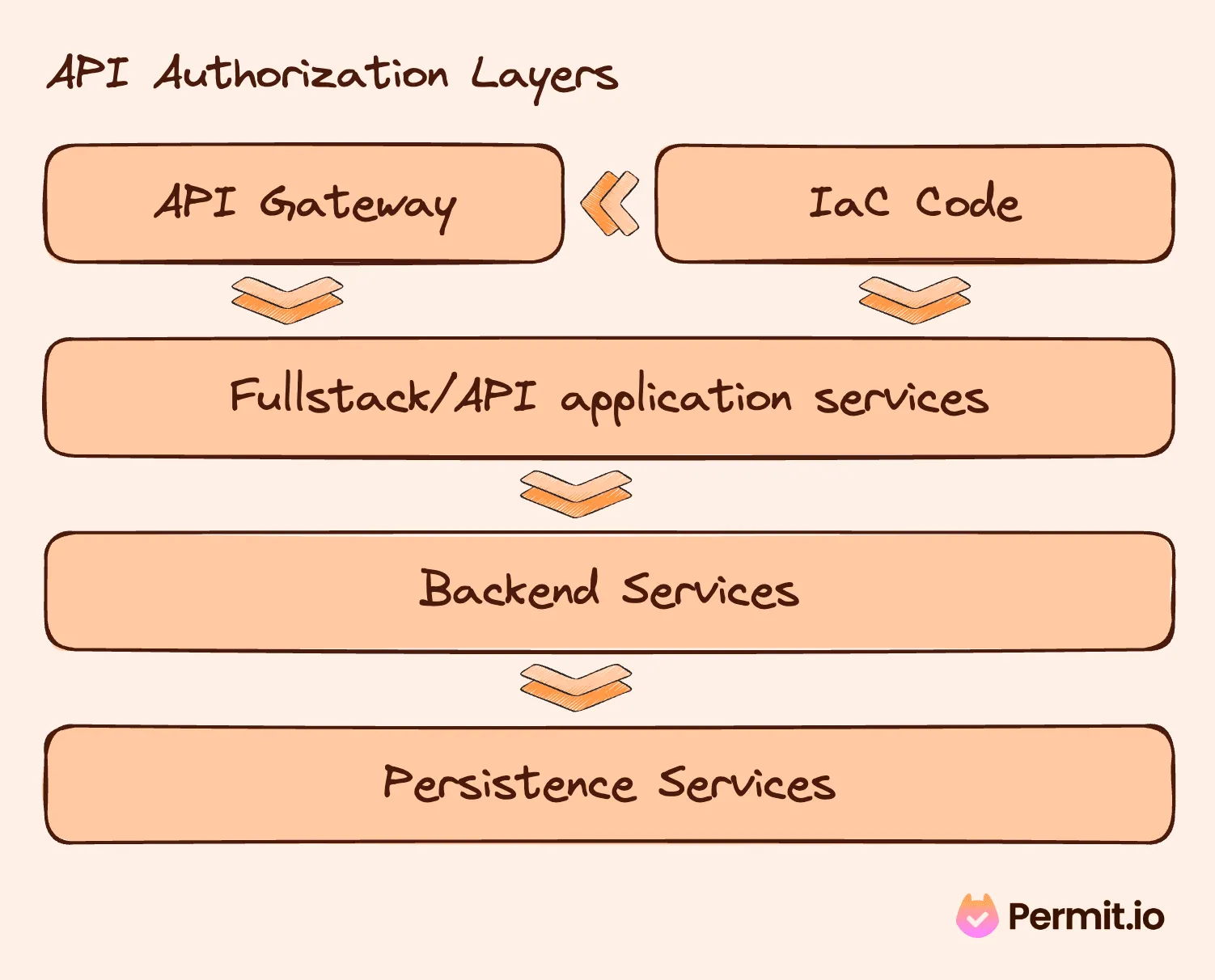
Authorization in an API ecosystem can be enforced at various layers, each having unique control mechanisms:
Understanding these layers and how to enforce authorization at each one is essential for maintaining a secure and reliable API.
While JSON Web Tokens (JWT) and OAuth scopes are fundamental to API security, they have limitations. JWT claims and OAuth scopes lack dynamic responsiveness to policy changes and may not provide comprehensive data for nuanced authorization decisions. They should be considered starting points for authorization but not the sole decision-making authority.
Policy as Code represents a fundamental change in how authorization policies are defined and managed. It allows for creating, testing, and deploying security policies as code, leading to better governance, transparency, and version control. Open Policy Agent (OPA) is a prime example, with its Rego language offering a powerful tool to define and manage policies for API authorization. Another example is AWS Cedar, which provides an application-centric policy language.
Here's a Cedar code example of a healthcare ABAC policy 👇🏻
permit (
principal,
action == HealthCareApp::Action::"createAppointment",
resource
)
when {
(context.referrer in HealthCareApp::Role::"doctor" && resource.patient == principal) ||
principal in HealthCareApp::Role::"admin"
};
Testing is critical to policy management, especially in dynamic environments where policies change frequently. Using a test environment for policy testing, especially with tools like OPAL (Open Policy Administration Layer), helps ensure policies work as intended before being deployed in production. This practice not only minimizes disruptions but also ensures compliance and security.
OPAL is an open-source tool that operates as a dynamic layer for policy engines like Open Policy Agent (OPA) and AWS' Cedar Agent. It detects real-time policy and data changes, ensuring policy agents are consistently up to date. This synchronization extends across various services, such as APIs, databases, and SaaS solutions.
Please consider supporting our open-source work by giving OPAL a star on GitHub.
Consistency in decision-making across API layers is crucial. Policy as Code engines, which can operate at various levels (like Envoy, Kong, and application code), ensure a single source of truth for all authorization decisions. This uniformity simplifies management, reduces errors, and enhances security.
Ensuring a uniform decision-making process across all API layers is not just about simplicity; it's about creating a cohesive security environment. Whether it's enforcing policies at the gateway or within the application code, a singular decision framework minimizes discrepancies and strengthens security protocols. This approach, facilitated by advanced tools like OPA, ensures that whether a request comes through a mobile app, a web service, or an internal microservice, it's subject to the same rigorous authorization checks.
The importance of a centralized audit system in API authorization cannot be overstated. It's the cornerstone of understanding not just what decisions were made but why they were made. By leveraging the capabilities of Policy as Code and tools like OPAL, organizations can gain insights into the effectiveness of their authorization strategies, identify potential security gaps, and ensure compliance with regulatory requirements. This level of oversight is crucial in a landscape where data breaches and unauthorized access can have significant repercussions.
Decoupling enforcement and decision-making in API authorization enhances security and scalability. Decentralized enforcement ensures that decisions are made close to the action point, reducing latency and load on central systems. OPAL exemplifies this approach, centralizing configuration while decentralizing decision-making and enforcement. This architecture enhances security and agility in API authorization practices.
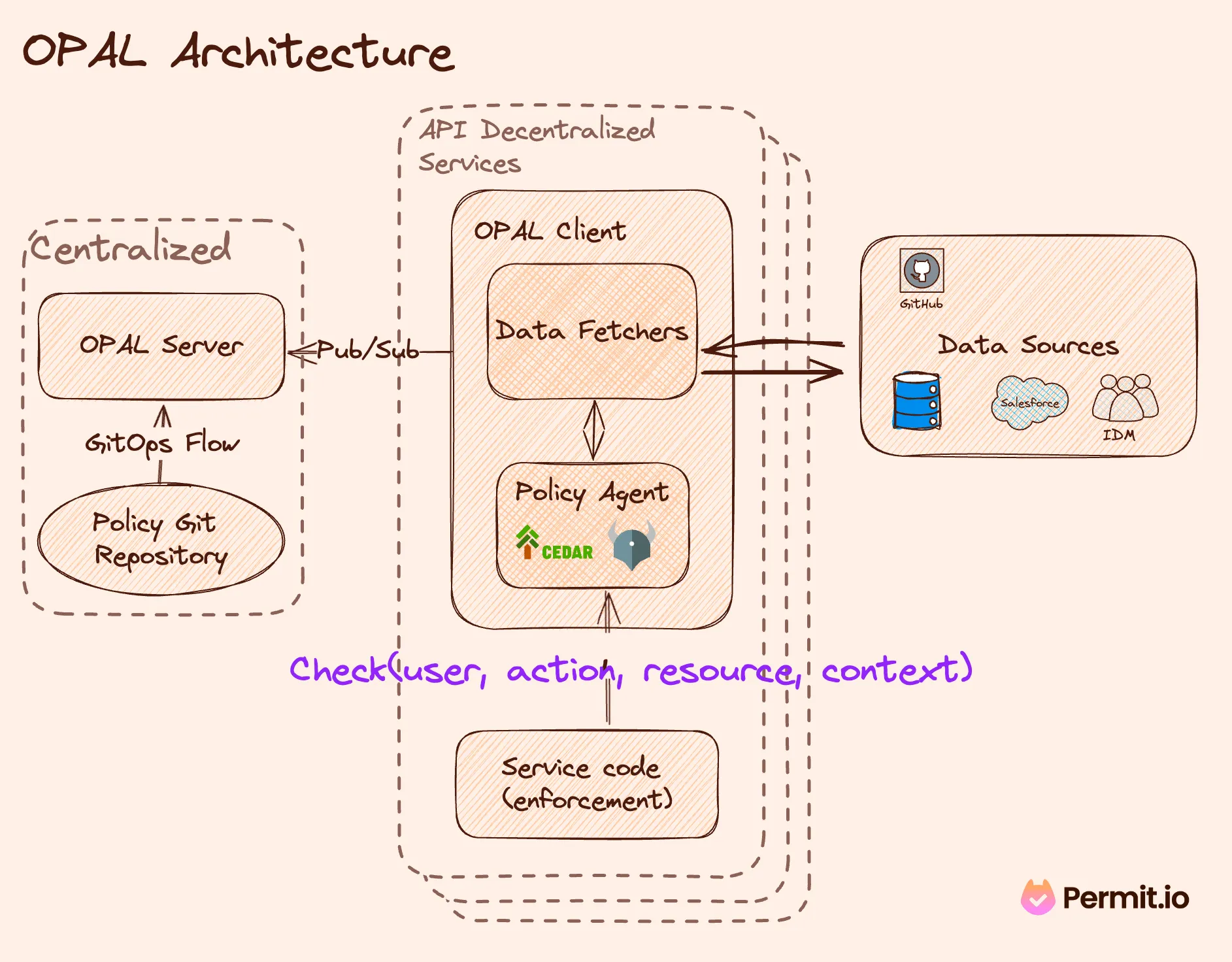
In API authorization, tools like Permit.io and OPAL represent the cutting edge. Permit.io, with its OPAL-based solution, offers a robust, scalable, and flexible framework for managing API authorization. By centralizing configuration, decentralizing enforcement, and providing comprehensive audit capabilities, these tools empower developers to implement best practices in API authorization. Engaging with the OPAL community on GitHub and exploring Permit.io's offerings are excellent starting points for those seeking to explore these advanced capabilities.

Application authorization enthusiast with years of experience as a customer engineer, technical writing, and open-source community advocacy. Comunity Manager, Dev. Convention Extrovert and Meme Enthusiast.