45 Questions to Ask Yourself Before Modeling Authorization

- Share:





2938 Members
Authorization is part of every modern application, ensuring users can only access the resources they are permitted to. While this might sound rather straightforward, considering how complex modern applications are, ensuring the right people get the right access to the right places is far from easy.
Before you start building, whether you are planning to build your own solution from scratch or use an existing authorization as a service solution, there are some crucial questions you must ask yourself when planning your implementation.
We see these questions being asked repeatedly on Reddit, StackOverflow, and in our own community dedicated to helping people build authorization systems. In order to make sure you have everything covered, we gathered them together in one place.
It doesn't matter whether you're upgrading an existing authorization system (From monolith to microservices-based, for example) or creating an authorization for a new application from scratch - these are the most critical questions you should ask yourself before modeling your authorization implementation.
If you have an existing implementation -
The first step in designing an authorization layer is determining the resources to which you need to manage access. Each type of resource and its place in the overall structure of your application might require you to utilize a different type of authorization model (RBAC, ABAC, ReBAC, or a combination of them).
It is important that you familiarize yourself with the available policy models out there, their pros and cons, and try to assess which ones are the best fit for your application.
Authorization policies should be flexible and accessible while remaining secure. It is common for various stakeholders (Product, Security, Compliance, Sales, Support etc.) to require a certain level of access to your authorization layer, being able to author and edit policies, and having these policies take immediate effect in the system.
Facilitating this need can’t come as an afterthought to building your authorization layer, and should be considered from day one. Utilizing Policy-as-code for this endeavor facilitates automation and integration into CI/CD pipelines, enabling faster deployment and iteration of policies while keeping all the best practices of code deployment in place.
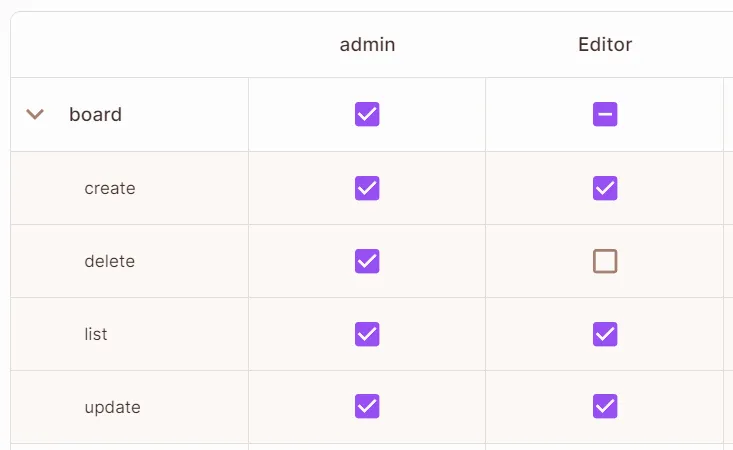
The Permit.io UI allows you to define policy via a UI that generates policy as code for you in your language of choice.
Effective user and data management ensures the authorization system is both accurate and responsive. Handling dynamic data efficiently can enhance the system's adaptability and responsiveness to real-time changes.
This can be achieved by using tools like Open Policy Administration Layer (OPAL), which helps keep your authorization layer updated in real-time with data and policy updates. This OSS includes two important features:
A centralized management system helps maintain consistency and integrity of policies across all platforms. Dynamic policies that adapt to real-time data ensure that access control is always relevant and secure. Centralization of your policy decisions can be achieved by using Policy Engines such as Open Policy Agent vs AWS Cedar. It is important to choose the policy engine and policy language that best suits your needs.
Quality logging and auditing capabilities are essential for compliance and security. They help track access patterns and detect anomalies, ensuring that your application meets regulatory standards and effectively manages risk.
A well-integrated system reduces maintenance overhead and avoids bottlenecks as your application scales. Consider the long-term impact of potential system changes to ensure sustainability.
Minimizing latency and maximizing reliability are critical for maintaining user satisfaction and trust. Efficient performance management ensures that security measures do not impede the application’s responsiveness.
Having an authorization layer that monitors access to the app’s authorization layer is crucial. It prevents unauthorized changes from being made to the authorization layer and ensures that any potential breaches are quickly identified and addressed.
Choosing the right technology stack for authorization and authentication can greatly affect both the system's effectiveness and the developer's ease of implementation. Understanding the limitations of current tools can guide future improvements and integrations.
The IAM landscape, as well as the potential security risks involved are constantly changing. This means we must keep our system current and adaptable. Implementing a process for ongoing assessment and improvement can help address emerging security challenges and incorporate advancements in technology. Regular updates, guided by the latest security research and compliance demands, ensure that your system not only meets current standards but is also prepared for future requirements. This approach reduces vulnerabilities and ensures that your authorization system evolves in step with both technological innovations and changes in the regulatory environment.
Building and managing an effective authorization system requires a thoughtful approach that balances security, usability, and performance. By considering these detailed questions, you can ensure your authorization system is strong, compliant, and ready for the challenges of modern application development.

Application authorization enthusiast with years of experience as a customer engineer, technical writing, and open-source community advocacy. Comunity Manager, Dev. Convention Extrovert and Meme Enthusiast.